eCryptfs is an encrypted file system that works at the file system level. In this post I am going to cover the basic usage of eCryptfs and some of the situations you may want to think about using a encrypted file system.
What is an encrypted file system?
File system encryption protects information by converting files and directories that exist on a file system into an unreadable format. To access the files and decipher the information afterward a passphrase is required.
Another related technology is full disk encryption which can be implemented using encfs on Linux. This differs from file system level encryption by encrypting the full disk or partition that the file system containing data resides.
Why would I care about this?
Everyone has some data that they would prefer is kept confidential such electronic receipts, account information, banking information etc. Devices do get lost and stolen at times so encryption so its best confidential data is protected.
Using eCryptfs with Debian
I use Debian on a RaspberryPi powered system at home which is connected to a removable hard drive to which my important information is backed up to using rsync & ssh. So in this post I am going to cover off the process of encrypting the backups with eCryptfs on a system running Debian. The general process is going to be the same in other distributions but the exact steps may vary.
To get started open a terminal and elevate your privileges to root and make sure the package list available to the system is up to date.
sudo su
apt-get update
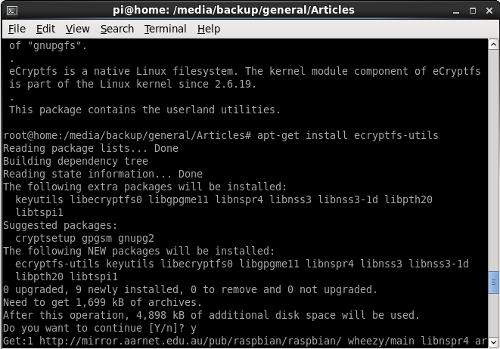
Install the utilities for working with eCryptfs.
apt-get install ecryptfs-utils
You then need to ensure the eCryptfs kernel module is loaded with lsmod.
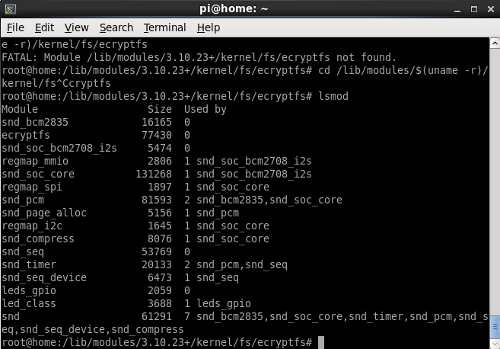
Note: On the RaspberryPi I was using the module was not loaded by default so I had to execute first:
cd /lib/modules/$(uname -r)
modprobe ./kernel/fs/ecryptfs
Now to encrypt a directory on the file system for an example. First create a directory that you would like to contain your encrypted data:
mkdir notes
Then we need to mount mount the newly created directory as a eCryptfs so the files are encrypted.
mount -t ecryptfs notes notes
Then you will be run though a few questions about the setup.
Select key type to use for newly created files:
1) passphrase
2) tspi
Selection: 1
Passphrase:
Select cipher:
1) aes: blocksize = 16; min keysize = 16; max keysize = 32
2) blowfish: blocksize = 8; min keysize = 16; max keysize = 56
3) des3_ede: blocksize = 8; min keysize = 24; max keysize = 24
4) twofish: blocksize = 16; min keysize = 16; max keysize = 32
5) cast6: blocksize = 16; min keysize = 16; max keysize = 32
6) cast5: blocksize = 8; min keysize = 5; max keysize = 16
Selection [aes]:
Select key bytes:
1) 16
2) 32
3) 24
Selection [16]: 2
Enable plaintext passthrough (y/n) [n]: n
Enable filename encryption (y/n) [n]:
Attempting to mount with the following options:
ecryptfs_unlink_sigs
ecryptfs_key_bytes=32
ecryptfs_cipher=aes
ecryptfs_sig=9b8bcea9e0a5ce7c
WARNING: Based on the contents of [/root/.ecryptfs/sig-cache.txt],
it looks like you have never mounted with this key
before. This could mean that you have typed your
passphrase wrong.
Would you like to proceed with the mount (yes/no)? : y
Would you like to proceed with the mount (yes/no)? : yes
Would you like to append sig [9b8bcea9e0a5ce71] to
[/root/.ecryptfs/sig-cache.txt]
in order to avoid this warning in the future (yes/no)? : yes
Successfully appended new sig to user sig cache file
Mounted eCryptfs
Now if the mount command is execute we should the directory we executed against mounted as a ecrypt file system.
Further Reading: